1.5.11. Token info#
When you select one token, you can choose “Token Info” to view details about the selected token.
In the Web UI you can click the button above the token view tab.
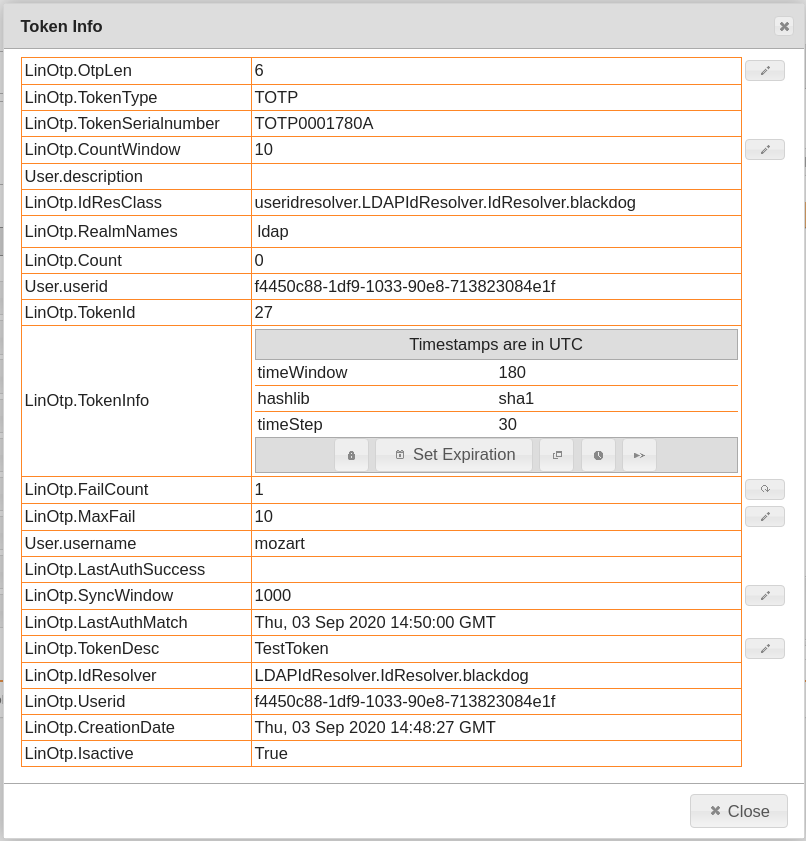
Detailed information about the token can be viewed in the Token Info dialog#
The displayed information reflect the database token table.
LinOtp.OtpLenThis is the length of the OTP value. The OTP value will be truncated to this length. Also, during authentication this value is used to split the entered credential into the OTP PIN and the OTP value.
LinOtp.TokenTypeThis is the internal type of the token. The type determines the TokenClass, that will be used to calculate the OTP value.
The list of the supported types is constantly increasing. Those types can be: HMAC, TOTP, mOTP, SMS, SPass, RADIUS, Remote…
Note
The type only specifies the type of algorithm to validate the OTP value or the way to distribute the OTP value. So the type “hmac” can be an SafeNet eToken PASS, a Feitian Token, a YubiKey and any other soft token, that uses the hmac (HOTP) algorithm.
LinOtp.TokenSerialnumberThis is a unique serial number of this very token.
The serial number also usually indicates the type of the token.
For OATH compliant tokens the first two letters specify the vendor.
Note
LinOTP’s own tokens will always start with “LS”.
The next two letters may specify the type of the token like:
LSSM: LinOTP SMs token
LSRE: LinOTP REmote token
LSRA: LinOTP RAdius token
LSO2: LinOTP Ocra2 token
LinOtp.CountWindowThis is the window where the LinOTP server searches a matching counter to validate the OTP value.
User.descriptionis a variable field that gets blended in from the UserIdResolver. The contents depends on the specific UserIdResolver implementation.
LinOtp.IdResolverClassThis is the UserIdResolver, where to user, to whom the token is assigned, is located.
LinOtp.RealmNamesThis is the list of realms in which the token is put.
LinOtp.CountThis is the counter of event based tokens.
User.UseridThis is the unique identifier to find the user in the given UserIdResolver.
LinOtp.TokenIdThis is the internal database id of the token.
LinOtp.TokenInfoThis is a field that holds many additional information like the type of the hash library used with the OATH algorithm or special information about time based TOTP tokens.
Also in this field the validity period of the token is stored. The validity period determines till when a token may be used and starting from which date a token may be used. E.g. this is used for the lost tokens (see Lost token).
LinOtp.Failcountsee
MaxFailLinOtp.MaxFailThis settings corresponds with the
Failcount. TheFailcountgets increased, when the user fails to authenticate with this token. When theFailcountreachesMaxFailthe user can not authenticate with this token anymore. (see Reset fail counter)User.usernameThis is the username (login name) of the user to whom the token is assigned.
LinOtp.LastAuthSuccessTime to use this token the last time it was successfully authenticated. Activated and thus visible are the additional timestamps (CreationDate, LastAuthMatch, LastAuthSuccess) here under
Log usage timestamps in token.SyncwindowWhen doing a resync (either manually or automatic) the fitting counter is searched for in this window.
LinOtp.LastAuthMatchTime at which this token was checked in an authentication or similar process. Several tokens of a user can be checked (multiple challenges).
TokenDescThis is the token description. Using the API it is possible to set the description to some thing of your needs. This is usually set to some kinds like “web enrolled”, “temporary replacement” or if it is an SMS token to the mobile phone number.
This field has no functional purpose.
LinOtp.IdResolverFull name of the UserIdResolver where the user of this token exists.
LinOtp.UseridThis is the unique identifier to find the user in the given UserIdResolver.
LinOtp.CreationDateTime at which this token was created.
LinOtp.IsActiveThis is the flag that indicates it the token is enabled or disabled.
